“My little birds are everywhere, even in the North, they whisper to me the strangest stories.” – Lord Varys Meet Whispers, an advanced static code analysis tool meticulously designed to parse various common data formats, unveiling hardcoded credentials, and identifying potentially hazardous functions. Whispers seamlessly integrates into both the command-line …
Read More »Identifying harmful activity on your captured traffic
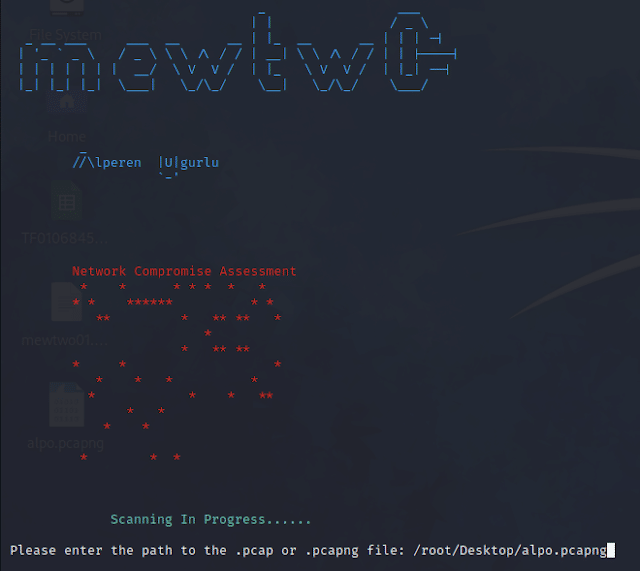
This Python script utilises Wireshark or TCPdump to analyse network traffic stored in a specified .pcap or .pcapng file. The objective is to detect potential malicious activities and attacks. The script covers a range of suspicious network behaviors, including: DNS Tunneling SSH Tunneling TCP Session Hijacking SMB Attack SMTP or …
Read More »Nyxt: Hacker’s Dream Browser
In the ever-evolving digital landscape, the demand for specialized tools and platforms has grown exponentially. For hackers and technology enthusiasts, having a browser that caters to their unique needs and empowers their capabilities is crucial. Enter Nyxt, an innovative and versatile web browser designed specifically with hackers in mind. With …
Read More »How to fix You can’t access this shared folder because your organization’s security policies block unauthenticated guest access error on Windows 11
If you have the following error on Windows 11 “You can’t access this shared folder because your organization’s security policies block unauthenticated guest access error” while accessing shared folder (in my case it was a shared folder on my Unraid NAS). Then Run window (Win + R) and typed …
Read More »Find Related Domains and Subdomains with assetfinder
assetfinder is a Go-based tool to find related domains and subdomains that are potentially related to a given domain from a variety of sources including Facebook, ThreatCrowd, Virustotal and more. assetfinder uses a variety of sources including those in the infosec space and social networks which can give relevant info: …
Read More » blackMORE Ops Learn one trick a day ….
blackMORE Ops Learn one trick a day ….