This Joint Cybersecurity Advisory uses the MITRE Adversarial Tactics, Techniques, and Common Knowledge (ATT&CK®) framework, Version 9. See the ATT&CK for Enterprise for all referenced threat actor tactics and techniques. The Cybersecurity and Infrastructure Security Agency (CISA) and the Federal Bureau of Investigation (FBI) are engaged in addressing a spearphishing …
Read More »Side-Channel Vulnerability Variants 3a and 4 – Spectre and Meltdown
On May 21, 2018, new variants of the side-channel central processing unit (CPU) hardware vulnerabilities known as Spectre and Meltdown were publicly disclosed. These variants—known as 3A and 4—can allow an attacker to obtain access to sensitive information on affected systems. Systems Affected CPU hardware implementations Description Common CPU hardware …
Read More »Brute Force Attacks Conducted by Cyber Actors
In a traditional brute-force attack, a malicious actor attempts to gain unauthorized access to a single account by guessing the password. This can quickly result in a targeted account getting locked-out, as commonly used account-lockout policies allow three to five bad attempts during a set period of time. During a …
Read More »Cyber Actors Target Home and Office Routers and Networked Devices Worldwide
DHS and FBI recommend that all SOHO router owners power cycle (reboot) their devices to temporarily disrupt the malware. Network device management interfaces—such as Telnet, SSH, Winbox, and HTTP—should be turned off for wide-area network (WAN) interfaces, and, when enabled, secured with strong passwords and encryption. Network devices should be upgraded …
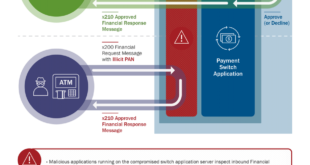
Read More »HIDDEN COBRA – FASTCash Campaign targeting banks
Since at least late 2016, HIDDEN COBRA actors have used FASTCash tactics to target banks in Africa and Asia. At the time of this TA’s publication, the U.S. Government has not confirmed any FASTCash incidents affecting institutions within the United States. FASTCash schemes remotely compromise payment switch application servers within …
Read More » blackMORE Ops Learn one trick a day ….
blackMORE Ops Learn one trick a day ….