Output your microphone to a remote computers speaker
Read More »Advanced Persistent Threat Activity Exploiting Managed Service Providers
Organizations should configure system logs to detect incidents and to identify the type and scope of malicious activity. Properly configured logs enable rapid containment and appropriate response. Response An organization’s ability to rapidly respond to and recover from an incident begins with the development of an incident response capability. An …
Read More »Setting Up A Free TLS/SSL Certificate With “Let’s Encrypt”
SSL (Secure Sockets Layer) is the standard security technology for establishing an encrypted link between a web server and a browser. This link ensures that all data passed between the web server and browsers remain private and integral. SSL is an industry standard and is used by millions of websites …
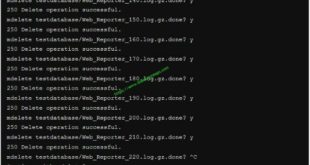
Read More »Mass delete files in FTP server
Ran into a little problem today, something I don’t really do often and something many would never do! Yeah, I’m talking about FTP .. the old pre-historic service of a thing that was originally RFC’d back in 1971. I had to mass delete files in FTP server, empty a folder …
Read More »Top 30 SSH shenanigans
Secure Shell (SSH) is a cryptographic network protocol for operating network services securely over an unsecured network. The best known example application is for remote login to computer systems by users. SSH provides a secure channel over an unsecured network in a client-server architecture, connecting an SSH client application with …
Read More » blackMORE Ops Learn one trick a day ….
blackMORE Ops Learn one trick a day ….