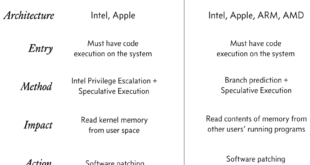
During the first week of January 2018, the world has been plunged into hot and anxious discussions concerning two newly discovered vulnerabilities in nearly all major ARM-based CPUs including smartphones, tablets, and some computers. The vulnerability itself even extends to the IBM’s POWER processors which run nearly all supercomputers! Starting …
Read More »Hacking remote desktop protocol using rdpy
RDPY is a Microsoft RDP Security Tool developed in pure Python with RDP Man in the Middle proxy support. This allows a user to record sessions and develop honeypot functionality. It supports both Microsoft RDP (Remote Desktop Protocol) protocol client and server side. RDPY supports standard RDP security layer, RDP …
Read More »Gain root access in macOS High Sierra #iamroot
It’s a rather embarrassing a bug that was discovered by developer Lemi Ergin that allows anyone to gain root access in macOS High Sierra with a blank password. Yes, all you need to do is just press enter enough times and you’re root. In fact everyone now using #iamroot just to …
Read More »Wireless WPA2 password cracking using KRACK attacks
We discovered serious weaknesses in WPA2, a protocol that secures all modern protected Wi-Fi networks. An attacker within range of a victim can exploit these weaknesses using key reinstallation attacks (KRACKs). Concretely, attackers can use this novel attack technique to read information that was previously assumed to be safely encrypted. …
Read More »Pay the Ransom or Face the Music – Hackers Threaten Apple Over iCloud Compromised Accounts
If you are an Apple user and thought that your data was secure, perhaps it’s time you retracted that thought. According to Motherboard, an Information and Technology Security magazine, a gang of hackers going by the name “Turkish Crime Family” allegedly claim a hold of over 200 million iCloud Compromised …
Read More » blackMORE Ops Learn one trick a day ….
blackMORE Ops Learn one trick a day ….