We discovered serious weaknesses in WPA2, a protocol that secures all modern protected Wi-Fi networks. An attacker within range of a victim can exploit these weaknesses using key reinstallation attacks (KRACKs). Concretely, attackers can use this novel attack technique to read information that was previously assumed to be safely encrypted. This can be abused to steal sensitive information such as credit card numbers, passwords, chat messages, emails, photos, and so on. The attack works against all modern protected Wi-Fi networks. Depending on the network configuration, it is also possible to inject and manipulate data. For example, an attacker might be able to inject ransomware or other malware into websites. This article discusses wireless WPA2 password cracking using KRACK attacks.
The weaknesses are in the Wi-Fi standard itself, and not in individual products or implementations. Therefore, any correct implementation of WPA2 is likely affected. To prevent the attack, users must update affected products as soon as security updates become available. Note that if your device supports Wi-Fi, it is most likely affected. During our initial research, we discovered ourselves that Android, Linux, Apple, Windows, OpenBSD, MediaTek, Linksys, and others, are all affected by some variant of the attacks. For more information about specific products, consult the database of CERT/CC, or contact your vendor.
The research behind the attack will be presented at the Computer and Communications Security (CCS) conference, and at the Black Hat Europe conference. Our detailed research paper can already be downloaded.
Table of Contents
Demonstration
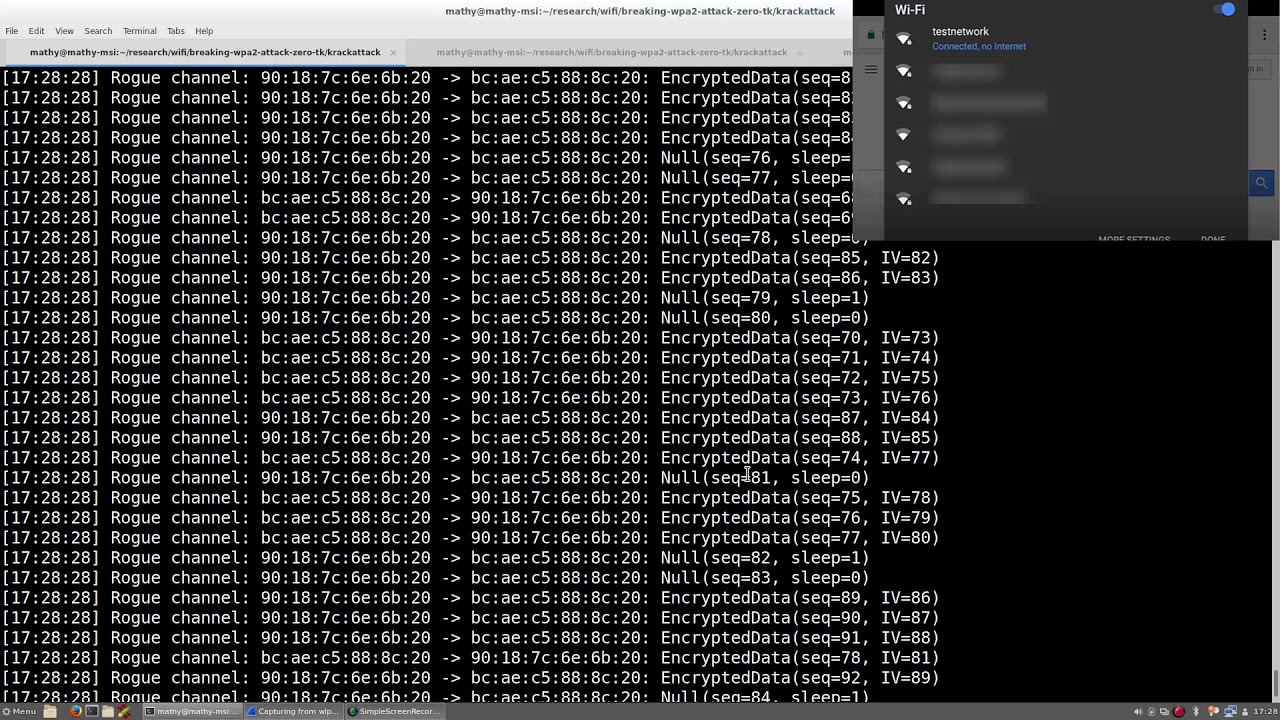
As a proof-of-concept we executed a key reinstallation attack against an Android smartphone. In this demonstration, the attacker is able to decrypt all data that the victim transmits. For an attacker this is easy to accomplish, because our key reinstallation attack is exceptionally devastating against Linux and Android 6.0 or higher. This is because Android and Linux can be tricked into (re)installing an all-zero encryption key. When attacking other devices, it is harder to decrypt all packets, although a large number of packets can nevertheless be decrypted. In any case, the following demonstration highlights the type of information that an attacker can obtain when performing key reinstallation attacks against protected Wi-Fi networks:
The research [PDF], titled Key Reinstallation Attacks: Forcing Nonce Reuse in WPA2, has been published by Mathy Vanhoef of KU Leuven and Frank Piessens of imec-DistriNet, Nitesh Saxena and Maliheh Shirvanian of the University of Alabama at Birmingham, Yong Li of Huawei Technologies, and Sven Schäge of Ruhr-Universität Bochum.
The team has successfully executed the key reinstallation attack against an Android smartphone, showing how an attacker can decrypt all data that the victim transmits over a protected WiFi. You can watch the proof-of-concept (PoC) video demonstration above.
“Decryption of packets is possible because a key reinstallation attack causes the transmit nonces (sometimes also called packet numbers or initialization vectors) to be reset to zero. As a result, the same encryption key is used with nonce values that have already been used in the past,” the researcher say.
The researchers say their key reinstallation attack could be exceptionally devastating against Linux and Android 6.0 or higher, because “Android and Linux can be tricked into (re)installing an all-zero encryption key (see below for more info).”
Tools
We have made scripts to detect whether an implementation of the 4-way handshake, group key handshake, or Fast BSS Transition (FT) handshake is vulnerable to key reinstallation attacks. These scripts are available on github, and contain detailed instructions on how to use them.
We also made a proof-of-concept script that exploits the all-zero key (re)installation present in certain Android and Linux devices. This script is the one that we used in the demonstration video. It will be released once everyone has had a reasonable chance to update their devices (and we have had a chance to prepare the code repository for release). We remark that the reliability of our proof-of-concept script may depend on how close the victim is to the real network. If the victim is very close to the real network, the script may fail because the victim will always directly communicate with the real network, even if the victim is (forced) onto a different Wi-Fi channel than this network.
Here’s another video demonstration of KRACK Attacks – Dr Mike Pound & Dr Steve Bagley on the Krack Attack discovered by researchers in Belgium.
WPA2 Vulnerabilities Details
The key management vulnerabilities in the WPA2 protocol discovered by the researchers has been tracked as:
- CVE-2017-13077: Reinstallation of the pairwise encryption key (PTK-TK) in the four-way handshake.
- CVE-2017-13078: Reinstallation of the group key (GTK) in the four-way handshake.
- CVE-2017-13079: Reinstallation of the integrity group key (IGTK) in the four-way handshake.
- CVE-2017-13080: Reinstallation of the group key (GTK) in the group key handshake.
- CVE-2017-13081: Reinstallation of the integrity group key (IGTK) in the group key handshake.
- CVE-2017-13082: Accepting a retransmitted Fast BSS Transition (FT) Reassociation Request and reinstalling the pairwise encryption key (PTK-TK) while processing it.
- CVE-2017-13084: Reinstallation of the STK key in the PeerKey handshake.
- CVE-2017-13086: reinstallation of the Tunneled Direct-Link Setup (TDLS) PeerKey (TPK) key in the TDLS handshake.
- CVE-2017-13087: reinstallation of the group key (GTK) while processing a Wireless Network Management (WNM) Sleep Mode Response frame.
- CVE-2017-13088: reinstallation of the integrity group key (IGTK) while processing a Wireless Network Management (WNM) Sleep Mode Response frame.
The researchers discovered the vulnerabilities last year, but sent out notifications to several vendors on July 14, along with the United States Computer Emergency Readiness Team (US-CERT), who sent out a broad warning to hundreds of vendors on 28 August 2017.
“The impact of exploiting these vulnerabilities includes decryption, packet replay, TCP connection hijacking, HTTP content injection, and others,” the US-CERT warned. “Note that as protocol-level issues, most or all correct implementations of the standard will be affected.”