Penetration testing (also called pen testing) is the practice of testing a computer system, network or Web application to find vulnerabilities that an attacker could exploit. Kali Linux Cheat Sheet for Penetration testers is a high level overview for typical penetration testing environment ranging from nmap, sqlmap, ipv4, enumeration, fingerprinting …
Read More »How to add RBL on Zimbra Server?
A DNS-based Blackhole List (DNSBL) or Real-time Blackhole List (RBL) is an effort to stop email spamming. It is a “blacklist” of locations on the Internet reputed to send email spam. The locations consist of IP addresses which are most often used to publish the addresses of computers or networks …
Read More »Get help when your device is CryptoLocked
Law enforcement and IT Security companies have joined forces to disrupt cybercriminal businesses with ransomware connections. The “No More Ransom” website is an initiative by the National High Tech Crime Unit of the Netherlands’ police, Europol’s European Cybercrime Centre and two cyber security companies – Kaspersky Lab and Intel Security …
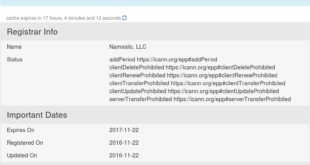
Read More »Shortest spam run ever – domaincop.org Domain Abuse Notice Spam
Woke up this morning and found two emails from domaincorp.org in my Inbox stating my domains are being used for spamming and spreading malware recently. Subject line contained “Domain Abuse Notice” which looked serious!
Read More »Top 30 SSH shenanigans
Secure Shell (SSH) is a cryptographic network protocol for operating network services securely over an unsecured network. The best known example application is for remote login to computer systems by users. SSH provides a secure channel over an unsecured network in a client-server architecture, connecting an SSH client application with …
Read More » blackMORE Ops Learn one trick a day ….
blackMORE Ops Learn one trick a day ….