Vulnerability scanning is a crucial phase of a penetration test and having an updated vulnerability scanner in your security toolkit can often make a real difference by helping you discover overlooked vulnerable items. For this reason, we’ve manually packaged the latest and newly released OpenVAS 8.0 tool and libraries for Kali Linux. Although nothing major has changed in this release in terms of running the vulnerability scanner, I wanted to give a quick overview on how to Install, setup, configure and run OpenVAS on Kali Linux
Table of Contents
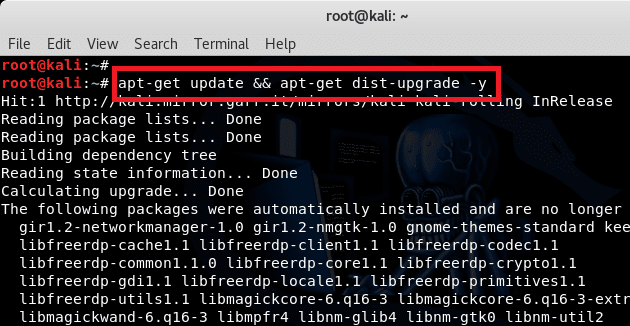
Setting up Kali for installing OpenVAS
If you haven’t already, make sure your Kali is up-to-date and install the latest OpenVAS. Once done, run the openvas-setup command to setup OpenVAS, download the latest rules, create an admin user, and start up the various services. Depending on your bandwidth and computer resources, this could take a while.
root@kali:~# apt-get update && apt-get dist-upgrade -y root@kali:~# reboot
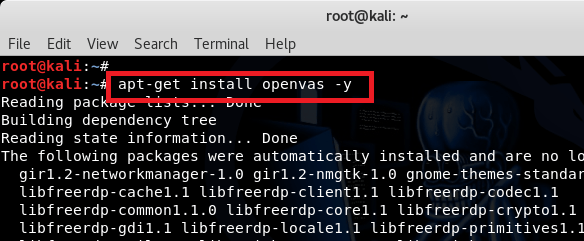
After the reboot has completed, you need to open terminal again and install OpenVAS.
root@kali:~# apt-get install openvas -y
This should take some time as the install is around 81.6MB assuming that none of the per-requisitities were ever installed. Sit back and keep reading this guide while the installation continues.
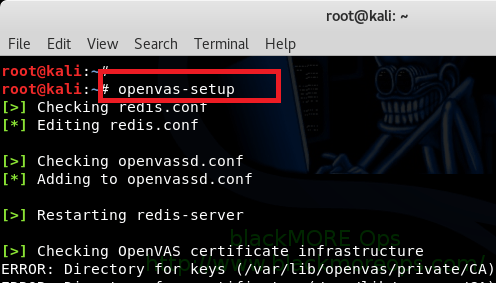
After the installation is finished, you need to run openvas-setup. This again will take a VERY long time as at this point it will download a lot of CVE, sync NVT’s, Vulnerabilities etc. This process also generates a certificate for HTTPS login to OpenVAS gui.
root@kali:~# openvas-setup [>] Checking redis.conf [*] Editing redis.conf [>] Checking openvassd.conf [*] Adding to openvassd.conf [>] Restarting redis-server [>] Checking OpenVAS certificate infrastructure ERROR: Directory for keys (/var/lib/openvas/private/CA) not found! ERROR: CA key not found in /var/lib/openvas/private/CA/cakey.pem [*] Creating OpenVAS certificate infrastructure Installed private key to /var/lib/openvas/private/CA/clientkey.pem. Installed certificate to /var/lib/openvas/CA/clientcert.pem. [>] Updating OpenVAS feeds [*] [1/3] Updating: NVT --2018-03-08 03:00:45-- https://dl.greenbone.net/community-nvt-feed-current.tar.bz2 Resolving dl.greenbone.net (dl.greenbone.net)... 89.146.224.58, 2a01:130:2000:127::d1 Connecting to dl.greenbone.net (dl.greenbone.net)|89.146.224.58|:80... connected. HTTP request sent, awaiting response... 200 OK Length: 34536678 (33M) [application/octet-stream] Saving to: ‘/tmp/greenbone-nvt-sync.dsrKn1A33f/openvas-feed-2018-03-08-4271.tar.bz2’ /tmp/greenbone-nvt- 100%[===================>] 32.94M 2.46MB/s in 13s ... ... ... 2018/adobe/ 2018/adobe/gb_adobe_flash_player_within_chrome_apsb18-01_lin.nasl 2018/adobe/gb_adobe_acrobat_dc_classic_apsb17-36_macosx.nasl.asc 2018/adobe/gb_adobe_acrobat_reader_2017_apsb18-02_macosx.nasl.asc 2018/adobe/gb_adobe_flash_player_within_chrome_apsb18-01_lin.nasl.asc 2018/adobe/gb_adobe_acrobat_dc_cont_apsb18-02_macosx.nasl ... ... ... ... Mar 08 03:04:15 kali systemd[1]: Starting Open Vulnerability Assessment System Manager Daemon... [*] Opening Web UI (https://127.0.0.1:9392) in: 5... 4... 3... 2... 1... [>] Checking for admin user [*] Creating admin user User created with password 'e432aa97-2fd3-4c1b-8c16-1166cbd19d70'. [+] Done
Checking for OpenVAS ports
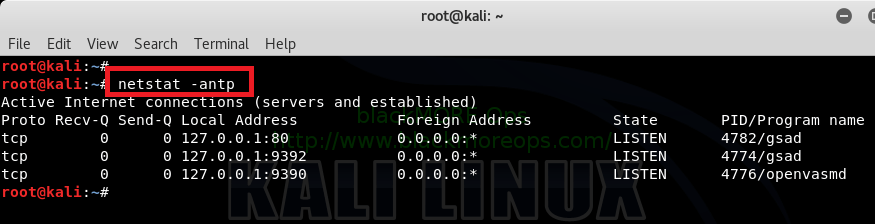
Once openvas-setup completes its process, the OpenVAS manager, scanner, and GSAD services should be listening:
root@kali:~# root@kali:~# netstat -antp Active Internet connections (servers and established) Proto Recv-Q Send-Q Local Address Foreign Address State PID/Program name tcp 0 0 127.0.0.1:80 0.0.0.0:* LISTEN 4782/gsad tcp 0 0 127.0.0.1:9392 0.0.0.0:* LISTEN 4774/gsad tcp 0 0 127.0.0.1:9390 0.0.0.0:* LISTEN 4776/openvasmd root@kali:~#
Note those ports? 9392 is for WebGUI/OpenVAS Web Interface.
Checking OpenVAS services
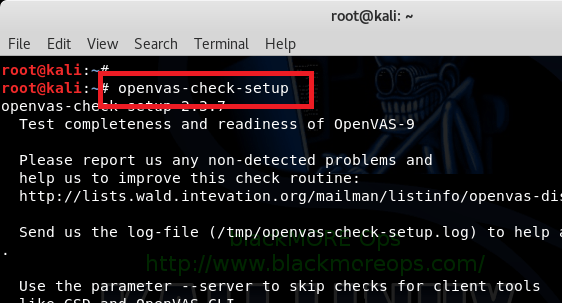
Most guides including the official guides would say to run openvas-start but I found it useful to run openvas-check-setup before launching OpenVAS just in case something went missing. For example, in my setup; note that this is a FRESH Kali Installation with Fresh OpenVAS Installation, I found 1 error about greenbone-scapdata-sync.
root@kali:~# openvas-check-setup
openvas-check-setup 2.3.7
Test completeness and readiness of OpenVAS-9
Please report us any non-detected problems and
help us to improve this check routine:
https://lists.wald.intevation.org/mailman/listinfo/openvas-discuss
...
...
...
ERROR: No OpenVAS SCAP database found. (Tried: /var/lib/openvas/scap-data/scap.db)
FIX: Run a SCAP synchronization script like greenbone-scapdata-sync.
ERROR: Your OpenVAS-9 installation is not yet complete!
Please follow the instructions marked with FIX above and run this
script again.
If you think this result is wrong, please report your observation
and help us to improve this check routine:
https://lists.wald.intevation.org/mailman/listinfo/openvas-discuss
Please attach the log-file (/tmp/openvas-check-setup.log) to help us analyze the problem.
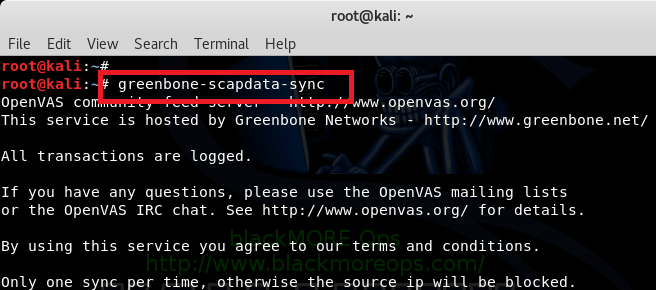
The fix is given in the error as well, simple run greenbone-scapdata-sync and it will sync OpenVAS SCAP database files.
root@kali:~# greenbone-scapdata-sync
OpenVAS community feed server - https://www.openvas.org/
This service is hosted by Greenbone Networks - https://www.greenbone.net/
All transactions are logged.
If you have any questions, please use the OpenVAS mailing lists
or the OpenVAS IRC chat. See https://www.openvas.org/ for details.
By using this service you agree to our terms and conditions.
Only one sync per time, otherwise the source ip will be blocked.
receiving incremental file list
./
nvdcve-2.0-2005.xml
18,282,318 100% 3.05MB/s 0:00:05 (xfr#1, to-chk=76/89)
...
...
...
oval/5.10/org.mitre.oval/v/family/windows.xml.asc
181 100% 0.34kB/s 0:00:00 (xfr#68, to-chk=0/89)
sent 10,379 bytes received 884,066,503 bytes 2,847,268.54 bytes/sec
total size is 926,410,667 speedup is 1.05
part 0 Done
part 1 Done
part 0 Done
part 1 Done
/usr/sbin/openvasmd
I have a really fast Internet connection, but this took some time! However after it finished, I ran openvas-check-setup again to ensure there’s to major errors.
root@kali:~# openvas-check-setup ... ... It seems like your OpenVAS-9 installation is OK.
This time it came back as OK. There were few warnings, if you want you can follow up on those.
Starting OpenVAS services
Now that we’ve configured OpenVAS, updated all NVT’s and Scrap Databases, we can launch OpenVAS. You can simply start all the necessary services by running openvas-start. 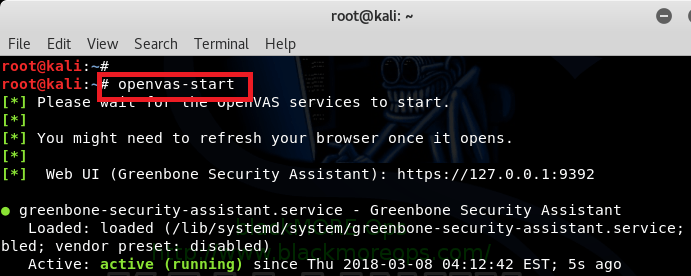
root@kali:~# openvas-start [*] Please wait for the OpenVAS services to start. [*] [*] You might need to refresh your browser once it opens. [*] [*] Web UI (Greenbone Security Assistant): https://127.0.0.1:9392 ● greenbone-security-assistant.service - Greenbone Security Assistant Loaded: loaded (/lib/systemd/system/greenbone-security-assistant.service; disabled; vendor preset: disabled) [*] Opening Web UI (https://127.0.0.1:9392) in: 5... 4... 3... 2... 1...
Setup OpenVAS User account and changing password
Remember the long password that was auto-created for admin user by default? You don’t? Neither do I!
I just feel that it’s a lot easier to set a manual password and create a new user from CLI. You can do that too: 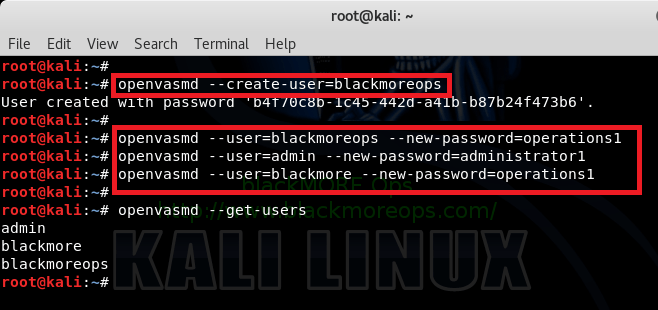
root@kali:~# root@kali:~# openvasmd --create-user=blackmore User created with password '19c29356-c59e-481a-8c3d-80225f80302b'. root@kali:~# openvasmd --create-user=blackmoreops User created with password 'b4f70c8b-1c45-442d-a41b-b87b24f473b6'. root@kali:~# root@kali:~# openvasmd --user=blackmoreops --new-password=operations1 root@kali:~# openvasmd --user=admin --new-password=administrator1 root@kali:~# openvasmd --user=blackmore --new-password=operations1 root@kali:~# root@kali:~# openvasmd --get-users admin blackmore blackmoreops root@kali:~#
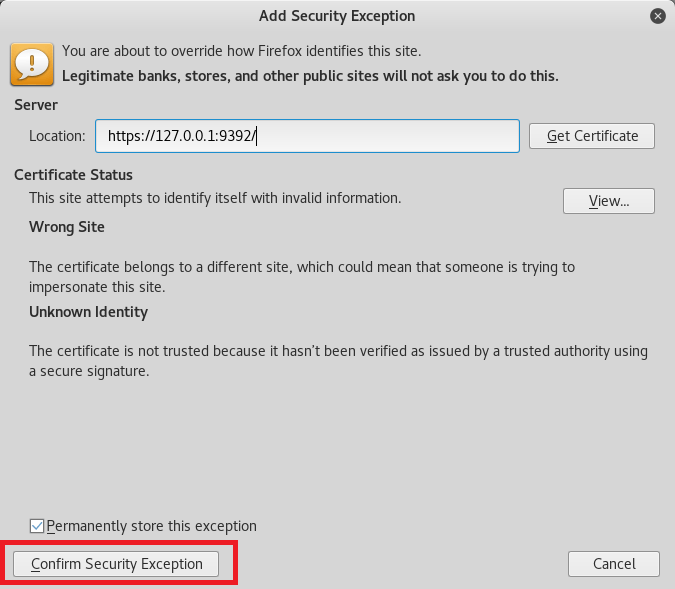
Connecting to the OpenVAS Web Interface
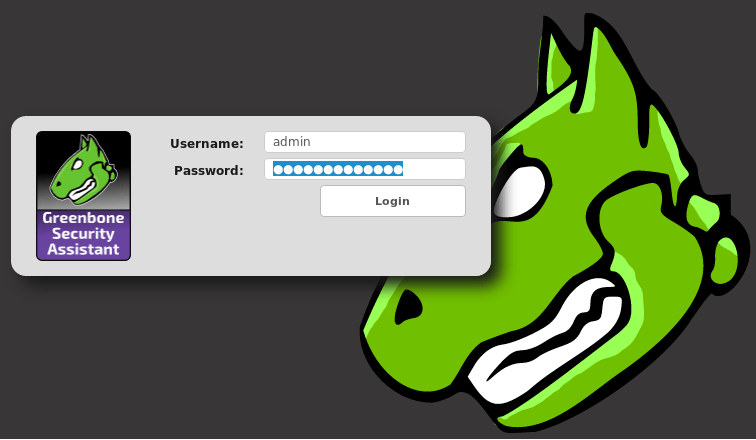
Point your browser to https://127.0.0.1:9392, accept the self signed SSL certificate and plugin the credentials for the admin user.
The admin password was generated during the setup phase. We’ve changed it but if you haven’t look through the outputs of simply reset it.
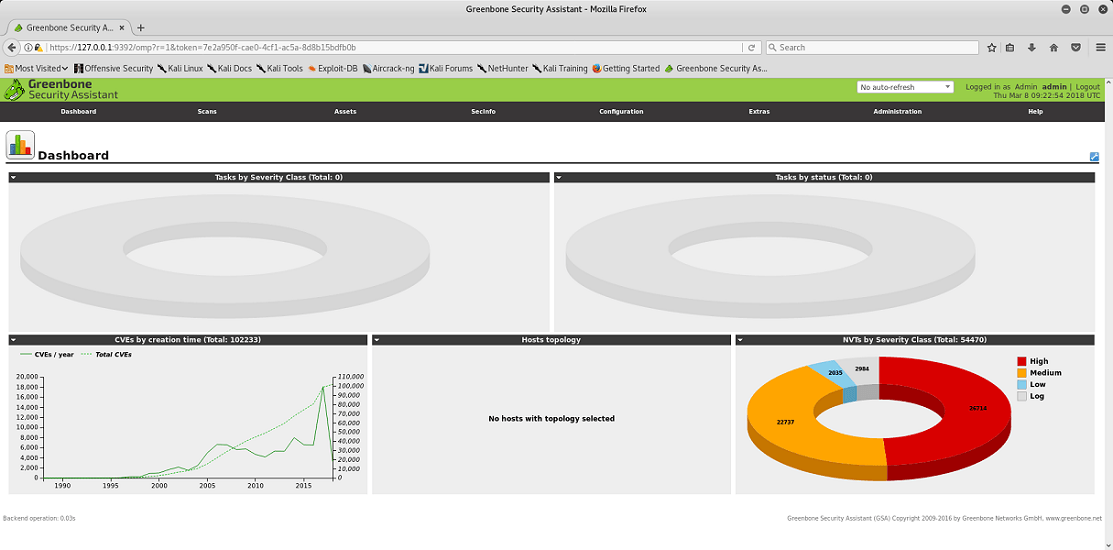
Type in Admin username and password or one of the new users you’ve setup and bang, you’re in.
OpenVAS is now ready for you to configure a scan-config and run a scan against a given IP or range. You are going to love that part!

6 comments
This worked in UBUNTU:
sudo apt-get install openvas
Thank you!
i keep getting error about pid1, so it wont start, 9392 is not showing in my netstat list, 9390 is though.
openvas-setup is now gvm-setup
I can access the’https://127.0.0.1:9392′ and the service is running, but when I running ‘ pvmd –create-user=XXX, it did not create the random password and ‘pvmd –get-users’ it`s nothing display there, am I miss something?
WOOT Openvas has renamed to gvm:
sudo apt install gvm -y
or
sudo gvm-setup
or
sudo gvm-feed-update
or
sudo gvm-start