This is a short guide on How to benchmark Pyrit
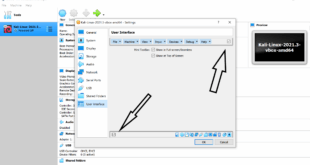
Assuming you managed to setup CUDA and Pyrit correctly, move on to the code section.
If not, go back and follow this guide: How to Install Nvidia Kernel Module Cuda and Pyrit
Benchmarking Pyrit:
# pyrit benchmark The Pyrit commandline-client (C) 2008 Lukas Lueg http://pyrit.googlecode.com This code is distributed under the GNU General Public License v3 The ESSID-blobspace seems to be empty; you should create an ESSID... Available cores: 'Standard CPU', 'Nvidia CUDA' Testing CPU-only core 'Standard CPU' (4 CPUs)... 1294.58 PMKs/s Testing GPU core 'Nvidia CUDA' (Device 'GeForce 460 GTX')... 5409.43 PMKs/s
Feel free to post your outputs in the comment section.
Background on Pyrit
Pyrit allows to create massive databases, pre-computing part of the IEEE 802.11 WPA/WPA2-PSK authentication phase in a space-time-tradeoff. Exploiting the computational power of Many-Core- and other platforms through ATI-Stream, Nvidia CUDA, OpenCL and VIA Padlock, it is currently by far the most powerful attack against one of the world’s most used security-protocols.
WPA/WPA2-PSK is a subset of IEEE 802.11 WPA/WPA2 that skips the complex task of key distribution and client authentication by assigning every participating party the same pre shared key. This master key is derived from a password which the administrating user has to pre-configure e.g. on his laptop and the Access Point. When the laptop creates a connection to the Access Point, a new session key is derived from the master key to encrypt and authenticate following traffic. The “shortcut” of using a single master key instead of per-user keys eases deployment of WPA/WPA2-protected networks for home- and small-office-use at the cost of making the protocol vulnerable to brute-force-attacks against it’s key negotiation phase; it allows to ultimately reveal the password that protects the network. This vulnerability has to be considered exceptionally disastrous as the protocol allows much of the key derivation to be pre-computed, making simple brute-force-attacks even more alluring to the attacker. For more background see this article on the project’s blog.
The author does not encourage or support using Pyrit for the infringement of peoples’ communication-privacy. The exploration and realization of the technology discussed here motivate as a purpose of their own; this is documented by the open development, strictly sourcecode-based distribution and ‘copyleft’-licensing.
Pyrit is free software – free as in freedom. Everyone can inspect, copy or modify it and share derived work under the GNU General Public License v3+. It compiles and executes on a wide variety of platforms including FreeBSD, MacOS X and Linux as operation-system and x86-, alpha-, arm-, hppa-, mips-, powerpc-, s390 and sparc-processors.
All code can be found at http://pyrit.googlecode.com
A more theoretical background of Pyrit can be found here.
Thanks for reading.
 blackMORE Ops Learn one trick a day ….
blackMORE Ops Learn one trick a day ….
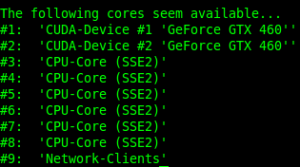
Without CAL++
After CAL++ it’s better … See comments here How to install CAL++ in Kali Linux?
Running benchmark (206050.5 PMKs/s)… –
Computed 206050.49 PMKs/s total.
#1: ‘CPU-Core (SSE2/AES)’: 51512.2 PMKs/s (RTT 2.9)
#2: ‘CPU-Core (SSE2/AES)’: 51512.1 PMKs/s (RTT 2.8)
#3: ‘CPU-Core (SSE2/AES)’: 51512.2 PMKs/s (RTT 3.0)
#4: ‘CPU-Core (SSE2/AES)’: 51512.0 PMKs/s (RTT 3.0)
root@NSA:~#
w0w 0_o