This is the first in a series of blogs featuring a Palo Alto Networks CYBERFORCE Engineer and the business challenges they tackle. CYBERFORCE recognizes the best-of-the-best from the NextWave Partner Community; proven partner engineers who put the customer first, are trusted for their security expertise, and focus on preventing successful …
Read More »HIDDEN COBRA – FASTCash Campaign targeting banks
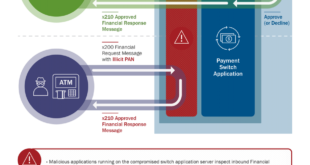
Since at least late 2016, HIDDEN COBRA actors have used FASTCash tactics to target banks in Africa and Asia. At the time of this TA’s publication, the U.S. Government has not confirmed any FASTCash incidents affecting institutions within the United States. FASTCash schemes remotely compromise payment switch application servers within …
Read More »Using Rigorous Credential Control to Mitigate Trusted Network Exploitation
Recommended best practices for mitigating this threat include rigorous credential and privileged-access management, as well as remote-access control, and audits of legitimate remote-access logs. While these measures aim to prevent the initial attack vectors and the spread of malicious activity, there is no single proven threat response. Using a defense-in-depth …
Read More »Automated Penetration Testing with APT2 Toolkit
APT2 is an Automated Penetration Testing Toolkit. This tool will perform an NMap scan, or import the results of a scan from Nexpose, Nessus, or NMap. The processesd results will be used to launch exploit and enumeration modules according to the configurable Safe Level and enumerated service information. All module …
Read More »Advanced Persistent Threat Activity Exploiting Managed Service Providers
Organizations should configure system logs to detect incidents and to identify the type and scope of malicious activity. Properly configured logs enable rapid containment and appropriate response. Response An organization’s ability to rapidly respond to and recover from an incident begins with the development of an incident response capability. An …
Read More » blackMORE Ops Learn one trick a day ….
blackMORE Ops Learn one trick a day ….