Windows 10 Rootkit
Read More »Search Gitlab For Sensitive Data and Credentials using GitLab Watchman
Search Gitlab For Sensitive Data and Credentials using GitLab Watchman
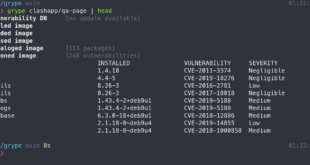
Read More »Vulnerability Scanner For Container Images & Filesystems
A vulnerability scanner for container images and filesystems. Easily install the binary to try it out. Works with Syft, the powerful SBOM (software bill of materials) tool for container images and filesystems.
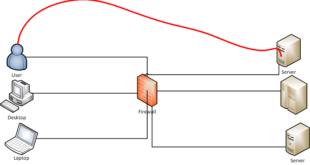
Read More »Use any Linux applications through a proxy (apt-get, wget etc)
It's pretty normal in many Organizations to use get servers to connect to Internet via a Proxy. In most cases it's for updating apt-get or yum via proxy. However, quite often you might need to download packages directly using wget or curl and setting up apt-get or apt via proxy, wget via proxy, curl via proxy is a pain. What if you could simply setup a Proxy and just use any applications to use that using a simply command? I faced this many times and hence writing this guide. Note that if you're only allowing apt-get via proxy then stick with configuring /etc/apt.conf or /etc/apt/conf.d/00proxy or something similar but if you need to allow different applications via a proxy then this method is best and simplest.
Read More »Inceptor – Template-Driven AV/EDR Evasion Framework
Modern Penetration testing and Red Teaming often requires to bypass common AV/EDR appliances in order to execute code on a target. With time, defenses are becoming more complex and inherently more difficult to bypass consistently. Inceptor is a tool which can help to automate great part of this process, hopefully requiring no further effort.
Read More » blackMORE Ops Learn one trick a day ….
blackMORE Ops Learn one trick a day ….