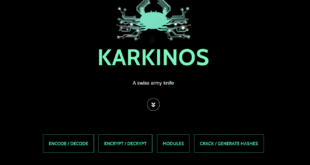
Penetration tools for beginners. Karkinos is a light-weight Beginner Friendly Penetration Testing Tool, which is basically a ‘Swiss Army Knife’ for pen-testing and/or hacking CTF’s.
Read More »Targeting websites with Password Reset Poisoning
Most of web application security vulnerabilities, leverage user input in ways that were not initially intended by their developer(s). Password Reset Poisoning is one such vulnerability, that leverages commonly unthought of headers, such as the Host header seen in an HTTP request: GET https://example.com/reset.php?email=foo@bar.com HTTP/1.1 Host: evilhost.com Notice the difference …
Read More »Setting up Damn Vulnerable Web Application (DVWA) – Pentesting Lab
Damn Vulnerable Web App (DVWA) is a PHP/MySQL web application that is damn vulnerable. Its main goals are to be an aid for security professionals to test their skills and tools in a legal environment, help web developers better understand the processes of securing web applications and aid teachers/students to …
Read More »124 legal hacking websites to practice and learn
Joe Shenouda is well known in The Netherlands as “The Netdetective” who has extensive experience in IT, ICS & Information Security as an international hands-on technical engineer, trainer, consultant & research fellow with a successful record in developing & leading technical corporate Cybersecurity programs for military & global organizations. He …
Read More »Publicly Available Tools Seen in Cyber Incidents Worldwide
Remote Access Trojan: JBiFrost First observed in May 2015, the JBiFrost RAT is a variant of the Adwind RAT, with roots stretching back to the Frutas RAT from 2012. A RAT is a program that, once installed on a victim’s machine, allows remote administrative control. In a malicious context, it …
Read More » blackMORE Ops Learn one trick a day ….
blackMORE Ops Learn one trick a day ….